Sophos Central: You can register HA devices with Sophos Central and manage them centrally. Both devices must be on 18.0 MR4. You must configure HA on the web admin console of XG Firewall. High availability: Improvements to FastPath offload for HA active-passive configurations. Sophos XG Firewall 4 Synchronized Security Security Heartbeat™ - Your firewall and your endpoints are finally talking Sophos XG Firewall is the only network security solution that is able to fully identify the user and source of an infection on your network and automatically limit access to other network resources in response. By: Sophos Latest Version: 18.0 MR4 Sophos XG Firewall is a next-generation firewall in an all-in-one solution. It combines advanced networking controls, with multiple layers of protection, and application controls in a single virtual firewall that scans, controls and reports on traffic entering and leaving a VPC. XG V18 benefits from all these enhancements but also receives extra attention with X18 MR4. This release brings enhancements to performance, security, reliability and the management experience. XG Firewall MR4 also enables great new Sophos Central Management capabilities, which is where we’ll begin: New Sophos Central Enhancements. Currently my sophos xg310 is running version SFOS 17.5.15 MR-15, and in the update firmware section on the firewall portal i see an option to download and install SFOS 18.0.4 MR-4. It seem to download and install just fine, but after install/reboot it keep reverting back to SFOS 17.5.15 MR-15 as active image instead of the 18.0.4.
Overview
This article describes how to configure IPSec VPN Client to Site so that remote VPN users can access the enterprise File Server system remotely. Configuration is done on Sophos XG firewall device with firmware version 18
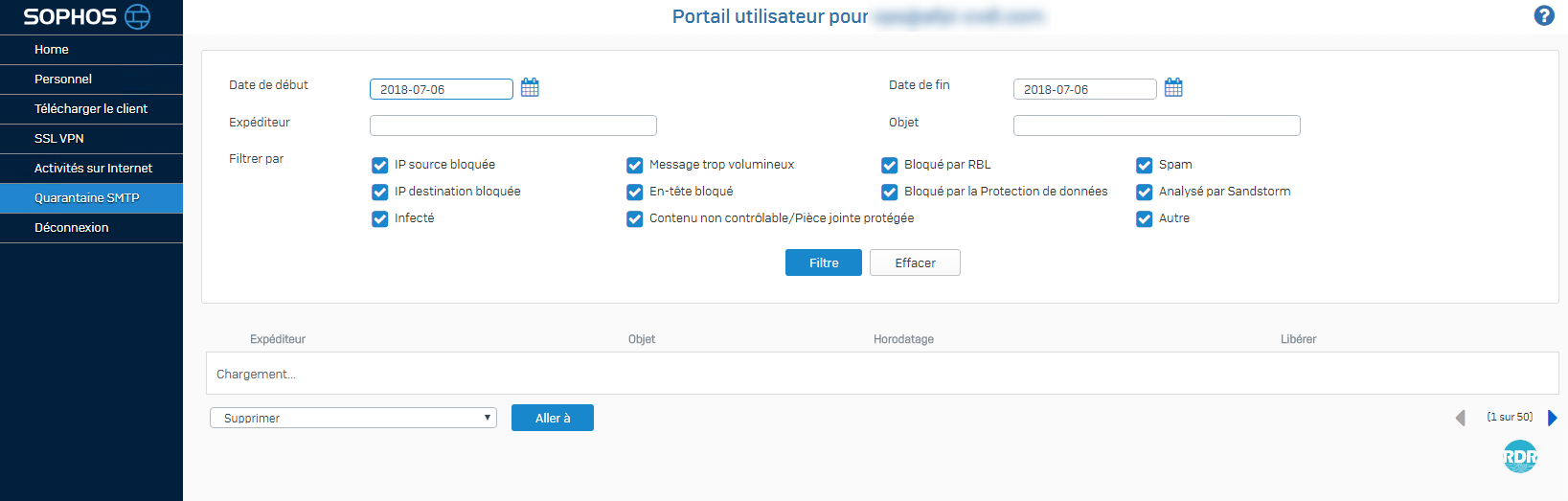
** When configuring SSL VPN, to install the application, you must get the installation source from the User Portal. As for IPSec VPN configuration, to install the application, you must use the installation file downloaded from the Admin account, and the Admin will share that installation file for the VPN user to install
Diagram
Summary of configuration steps
- Configure IPSec VPN Client to Site profile on Sophos XG
- Create IPSec VPN group
- Create IPSec VPN user
- Configure profile for IPSec VPN Client
- Download and install IPSec VPN Client
- Import configuration file to IPSec VPN Client
- Create firewall rule to allow communicate between IPSec VPN and LAN
- Configure NAT Port on Modem or Router
- Configure File Server
- Results
Configuration details
- Configure IPSec VPN Client to Site profile on Sophos XG
Login to Sophos XG by Admin account
1.1 Create IPSec VPN group
** Configuring group creation for IPSec VPN, it’s making easy for administrators to manage and user groups to apply policies according to the needs of the business
- Authentication -> Choose Group -> Click Add

- Create IPSec VPN group
- Group Name: Enter name for IPSec VPN group
- Surfing Quota: Select the network traffic you want
- Access Time: Select the access time you want
-> Click Save
1.2 Create IPSec VPN users
- Authentication -> Choose User -> Click Add
- Create IPSec VPN users
- Username: Enter name for VPN user
- Password: Enter password for IPSec VPN user
- Email: Enter manager’s email
- Group: Choose IPSec VPN group which was created before
-> Click Save
1.3 Configure profile for IPSec VPN Client
- VPN -> Choose Sophos Connect client
- In General settings
- Choose Enable
- In Interface: Choose WAN Port on Sophos XG
- In Authentication type: Choose Preshared key
- In Preshared key: Enter your preshared key
- In Allowed user: Choose IPSec VPN user which was created before
- In Client information
- In Name: Enter connection name
- In Assign IP from: Enter IP range provided for IPSec VPN Client
- In DNS server 1: Enter your DNS
- In DNS server 2: Enter your DNS
-> Click Apply -> Click Download to download IPSec VPN installation software -> Click Export connect to download configuration file
1.4 Download and install IPSec VPN Client
- Extract the installation application file
- Install SophosConnect.msi
- Install scadmin.msi
- Open Sophos Connect Admin -> Click Open to get profile which downloaded before
- You can adjust Target Host to IP WAN of Router or Modem
-> Click Save to save profile
** Saved the file with the .scx extension
1.5 Import configuration file to IPSec VPN Client
- Open Sophos Connect -> Click Import connection -> Choose .scx file
1.6 Create firewall rule to allow communicate between IPSec VPN and LAN
- Rules and Policies -> Click Add Firewall Rule
- Enter name
- In Source zones: Choose VPN
- In Source networks and devices: Choose Any
- In Destination zones: Choose LAN
- In Destination networks: Choose LAN network (Local subnet)
- Choose Match known users
- In Users and groups: Choose IPSec VPN group which was created before
-> Click Save
2. Configure NAT Port on Modem or Router
- We will Nat 2 port is 500 UDP and 4500 UDP
3. Configure File Server
- File sharing on File Server, share files folder for all users as well as VPN users to have access to read and write files
4. Results
- Make connection IPSec VPN Client to Site by opening the application installed on your computer
- Check IP address of IPSec VPN Client
- You access to File Server with File Server’s IP address is 172.16.16.19
- You type in address bar: 172.16.16.19
-> Done
YOU MAY ALSO INTEREST
Sophos has released the longly awaited MR-3 with many good fixes in the package, read all here:
RELEASE NOTES from Sophos:
Enhancements in v18 MR-3
Security enhancements:
Kagney linn karter twitter images.
- Several security and hardening enhancements – including SSMK (secure storage master key) for the encryption of sensitive data. Refer KB-000040174 for more details.
- Granular option to enable/ disable captcha authentication from CLI
VPN Remote Access enhancements:

- Increase in SSL VPN connection capacity across entire firewall line up; 6x increase for 2U HW. KB-000039345 is being updated with enhanced capacity.
- Group support for Sophos Connect VPN client
Cloud – AWS/ Azure/ Nutanix enhancements:
- Support for newer AWS instances – C5/ M5 and T3 (#)
- Support for CloudFormation Templates removing the need to run installation wizard in some cases (#)
- Virtual WAN Zone on custom gateway for post deployment single arm usage
- On single arm – single interface in AWS or Azure – admin can create multiple custom gateway and attached different zones to those gateways. This allows admin to create access and security rules for traffic going in to those zones.
- XG Firewall is now Nutanix AHV and Nutanix Flow Ready. XG Firewall has been validated to provide two modes of operation within Nutanix AHV infrastructure.
- Optimize cloud costs and improve security across multi-cloud environments with Cloud Optix. Automatic identification and risk-profiling of security and compliance risks across AWS, Azure and Google Cloud enables teams to fix security gaps and insecure deployments before they are compromised. Learn more.
(# available after a few days of release on community, once v18 MR-3 is available in the AWS marketplace)
Sophos Xg 18 Mr5
Central management enhancements:
- XG running in an HA configuration (either A-A or A-P) can now be managed by Sophos Central. Each firewall must be separately joined to the same Sophos Central account, and if grouped, both HA devices must be added to the same group.
- Audit trail went live under the task queue
Central Firewall Reporting enhancements: Mosfet 15a.
- Earlier this month, we have released Save, schedule, export & download reports. Refer community post here.
Issues Resolved:
- 34 field reported issues including RED & HA cluster issues (list below)
Note: Upgrading from v17.5 MR13/ MR14/ MR14-1 to v18 MR-3 is now supported.
Check out our recent blog and video series on how to make the most of the many great new capabilities in XG Firewall v18 such as the Xstream Architecture, TLS Inspection, FastPath acceleration, Zero-day threat protection, NAT, and much more.
We also have a new Sophos Techvids site for XG Firewall v18.
Get it now!
As usual, this firmware update is no charge for all licensed XG Firewall customers. The firmware will be rolled-out automatically to all systems over the coming weeks but you can access the firmware anytime to do a manual update through Licensing Portal. You can refer this article for more information on How to upgrade the firmware.
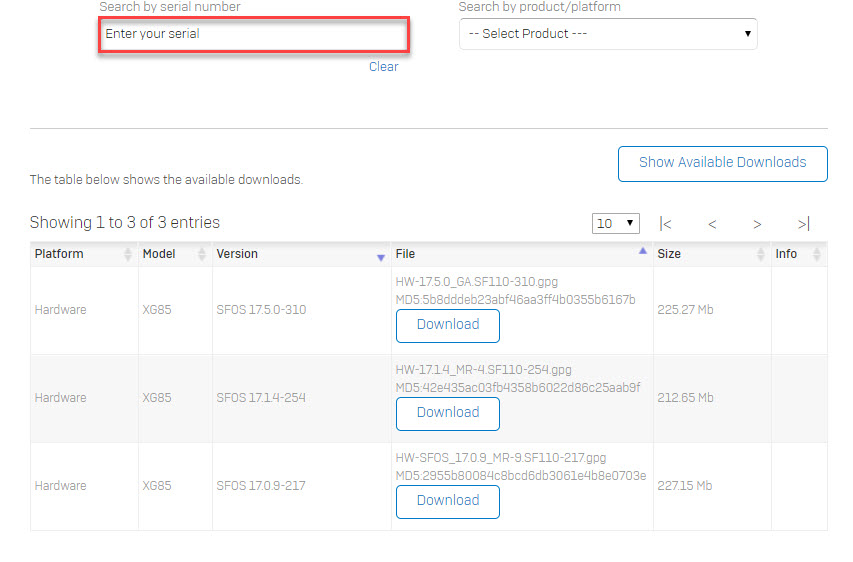
For fresh installations, the download links will be updated right here very soon.
Things to know before upgrading
Sophos Xg 18 Mr
Issues Resolved in v18 MR-3
- NC-58229 [Authentication] Sophos AV and Avira AV Pattern updates failing
- NC-51876 [Core Utils] Weak SSHv2 key exchange algorithms
- NC-58144 [DNS] XG self reporting its own lookups in ATP causing flood of events
- NC-54542 [Email] Email banner is added to incoming emails
- NC-59396 [Email] Blocked senders are able to send the mails
- NC-58159 [Firewall] Unable to ping the external IPs from auxiliary appliance console
- NC-58356 [Firewall] Direct proxy traffic doesn’t work when RBVPN is configured.
- NC-58402 [Firewall] Firewall reboots randomly.
- NC-59399 [Firewall] ERROR(0x03): Failed to migrate config. Loading default.
- NC-60713 [Firewall] Userportal hotspot voucher config gets timeout
- NC-60848 [Firewall] HA cluster both nodes rebooting unexpectedly
- NC-59063 [Firmware Management] Remove expired CAs from SFOS
- NC-44455 [HA] System originated traffic is not flow from AUX when SNAT policy configured for system originated traffic
- NC-62850 [HA] Filesystem oddity in /conf
- NC-58295 [IPsec] Dropped due to TLS engine error: STREAM_INTERFACE_ERROR
- NC-58416 [IPsec] IKE SA Re keying won’t be re-initiate itself after re-transmission time out of 5 attempts
- NC-58499 [IPsec] Sophos Connect Client ”IP is supposed to be added in the “##ALL_IPSEC_RW “
- NC-58687 [IPsec] IPsec tunnel not getting reinitiated after PPPoE reconnect
- NC-58075 [Netflow/IPFIX] Netflow data not sending interface ID
- NC-55698 [nSXLd] Not able to add new domain in custom category
- NC-62029 [PPPoE] PPPoE link does not reconnect after disconnecting
- NC-57819 [RED] XG Site to Site RED Tunnel disconnects randomly also with MR10 and v18
- NC-60240 [RED] Interfaces page is blank after adding SD-RED60 with PoE selected
- NC-61509 [RED] RCA s2s red tunnel static routes disappear on FW update
- NC-62161 [RED] RED connection with device becomes unstable after upgrading to v18.0 MR1 from v17.5 MR12
- NC-59204 [SFM-SCFM] Task queue pending but never apply with XG86W appliance
- NC-60599 [SFM-SCFM] Task queue pending but never apply due to no proper encoding
- NC-62304 [SFM-SCFM] The notification e-mail sent from the XG displays the wrong Central Administrator
- NC-61956 [UI Framework] WebAdmin Console and User Portal not accessible because space in certificate name
- NC-62218 [UI Framework] Post-auth command injection via User Portal 1/2 (CVE-2020-17352)
- NC-62222 [UI Framework] Post-auth command injection via User Portal 2/2 (CVE-2020-17352)
- NC-58960 [Up2Date Client] HA: IPS service observed DEAD
- NC-59064 [Web] Appliance goes unresponsive : Awarrenhttp high memory consumption
- NC-60719 [WebInSnort] DPI engine causing website to intermittently load slowly
Here are some direct links to helpful resources:
- Customer Training Portal (free Delta Training)
Source: https://community.sophos.com/xg-firewall/b/blog/posts/xg-firewall-v18-mr3
Related Posts